Re: Guest network routing, WLAN extension (e.g. WDS) etc
Posted: 14 Jul 2013, 17:54
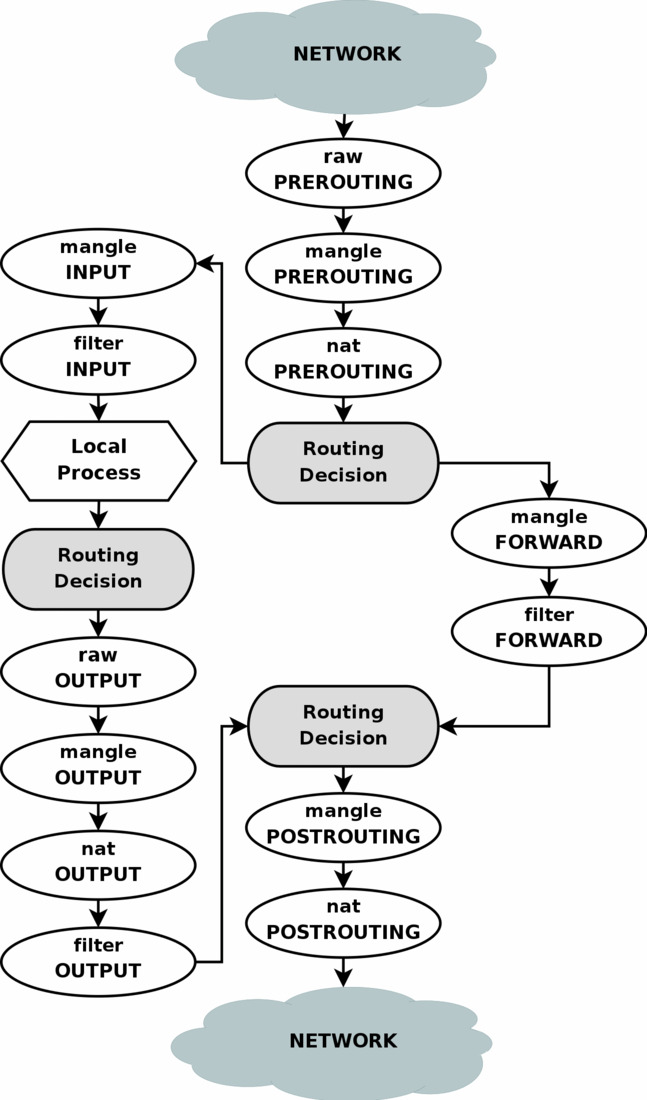
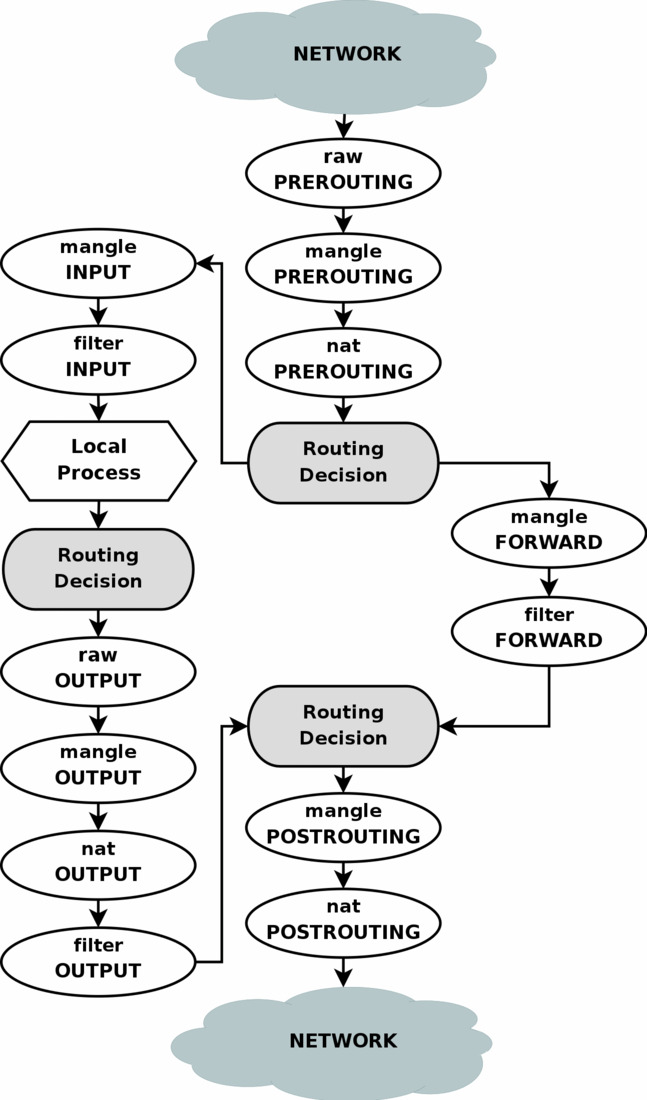
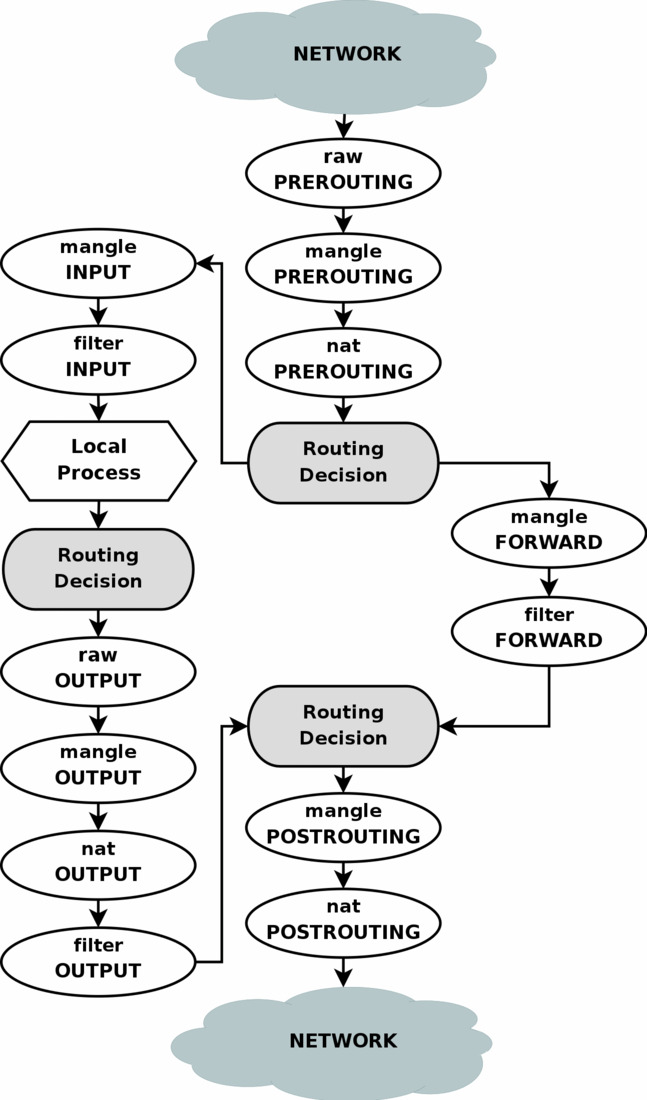
Maybe someone find the extensive tutoral at http://www.frozentux.net/documents/iptables-tutorial/ worth digging into.
Bubba community forum
https://forum.excito.com/
Okay, if you're sure than that simplifies the exercise and you can restrict yourself to adding a single firewall rule to the B3.gonk wrote:Thanks for the explanation but I'm not very interested in protecting other client machines on the internal network from guests trying to access them since they all have their software firewalls so disallowing access to the B3 is the topic for my request.
Every firewall rule that you add to the B3 will persist reboots. That is actually very dangerous and the reason why I did a rewrite of the standard INIT-V firewall script that makes this behaviour optional. You'll find it in the Howto section on this forum. I also created a package for it, by annoyingly DynDNS service flunked my hostname even though the updater returned a success every time and I can't get it back.gonk wrote:I'll try to figure out how to manually add firewall rules that will persist reboots and software updates.
That is correct. The basic principle of the home server is that everything that is on the LAN side is trusted and that everything on the WAN side should be stopped. Excito did not provide a way to disallow certain clients on the LAN side and that is probably a good thing since a mistake is easily made.gonk wrote:I'll try to figure out how to manually add firewall rules that will persist reboots and software updates.
In the B3 web interface you can only set up two type of firewall rules and neither match the need of blocking some internal clients from accessing the B3...
The first rule is very important and also I suggest that you do not edit /etc/network/firewall.conf directly-A INPUT -i eth0 -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -i br0 -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -i br0 -s 192.168.0.2 -j DROP
-A INPUT -i br0 -j ACCEPT
Code: Select all
iptables -I INPUT 4 -i br0 -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -I INPUT 5 -i br0 -s 192.168.0.2 -j DROPCode: Select all
iptables-restore < /etc/network/firewall.confCode: Select all
iptables-save > /etc/network/firewall.confCode: Select all
iptables -I INPUT 5 -i br0 -p tcp --dport 53 -j ACCEPT
iptables -I INPUT 5 -i br0 -p udp --dport 53 -j ACCEPTYes there is a lot of stuff that you can do with netfilter. Some useful, some just for play (mostly to annoy hackers). Most people will never use anything but a basic MASQUERADE rule and possibly a few filter (INPUT) rules though.gonk wrote:Maybe someone find the extensive tutoral at http://www.frozentux.net/documents/iptables-tutorial/ worth digging into.
Hi Gordon,Gordon wrote: Every firewall rule that you add to the B3 will persist reboots. That is actually very dangerous and the reason why I did a rewrite of the standard INIT-V firewall script that makes this behaviour optional. You'll find it in the Howto section on this forum. I also created a package for it, by annoyingly DynDNS service flunked my hostname even though the updater returned a success every time and I can't get it back.
I think you got my information wrong:Gordon wrote:Hi Ingo,
I have a similar cron job, logging on and prolonging the registered name twice every month.